News
In the News

Spring 2026 Senior Design Center’s Posters and Pies
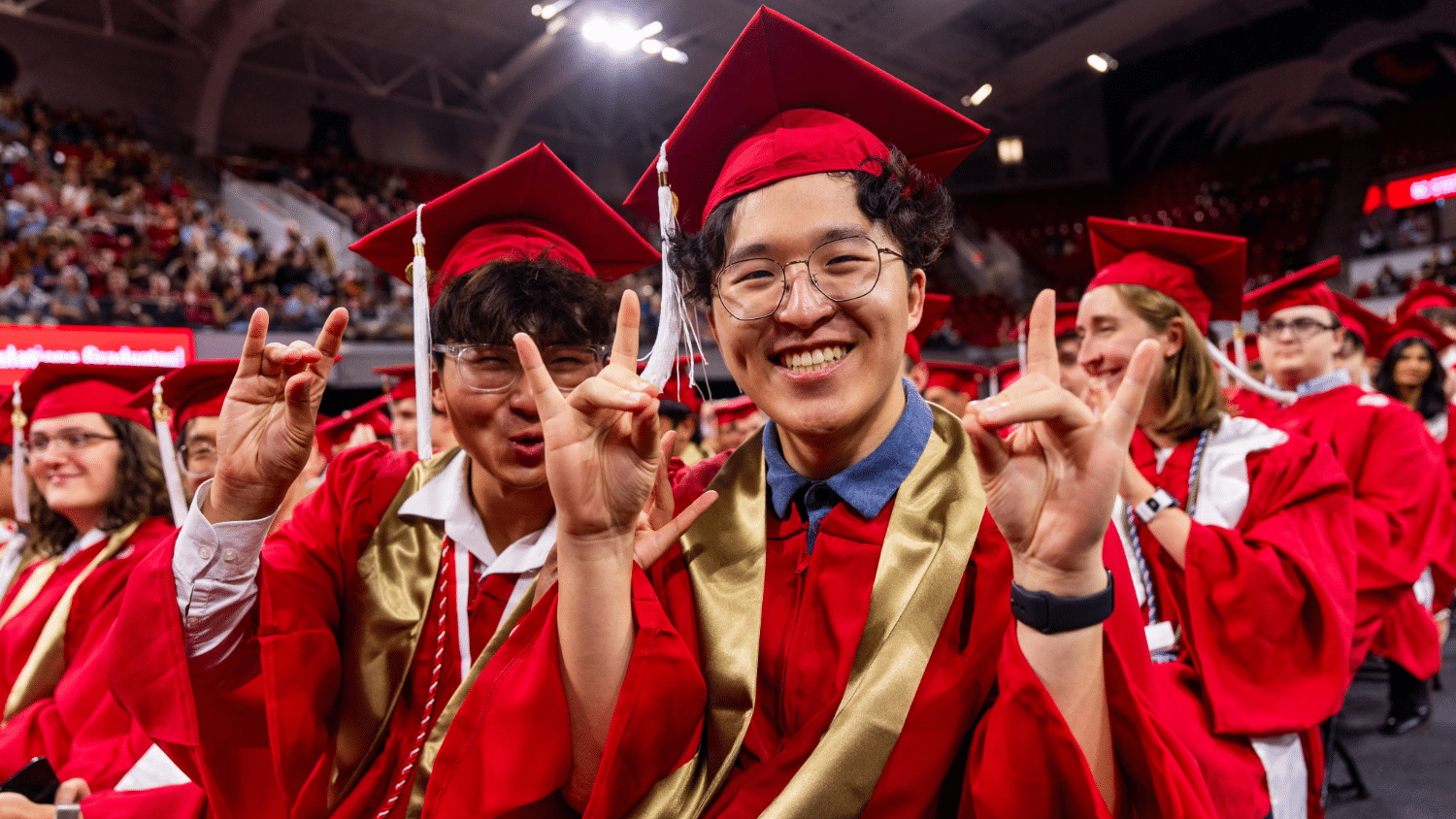
Congratulations to our Spring 2026 Graduates!

Welcoming Department of Computer Science Head Daphne Yao

Interns Tackle Ag Challenges With the N.C. PSI Makerspace

Three NC State Students Receive Goldwater Scholarships

Shahnewaz Leon, Sandeep Kuttal Receive Honorable Mention at ACM CHI

Jamie Jennings Wins PEP Award

Shandler Mason: Human-Centered Software Engineering

Jim Pfaendtner Selected as Next NC State Provost

2026 COE Awards Recognize Outstanding Staff and Faculty

Grad Programs Climb Atop the Rankings

