CSC News
Cyber Warriors
Computer scientists and engineers at NC State are winning the battle against hackers.
Source –NC State Engineering, NC State Engineering Foundation and Engineering Communications, Spring 2010
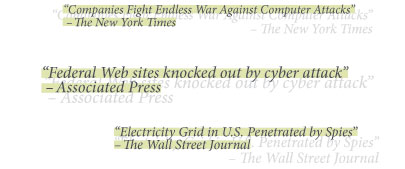
The headlines are ominous — and numerous.
There are many more just like them — warnings that personal data may be stolen, national security may be compromised, corporate information may fall into the wrong hands.
It’s the state of the world we live in today, and it’s for these reasons that NC State computer scientists and engineers are at the forefront of efforts to combat cyber-security threats. Through initiatives with government organizations, the military, health care providers and other industry partners, NC State works to keep us safe from hackers and train the next generation of computer security experts.
“This is a growth industry,” said Dennis Kekas, executive director of NC State’s Institute for Next Generation IT Systems. “There are going to be a lot of new jobs created in this new environment.”
To some degree, everyone who works with computers is involved with security. Even the most casual user has account passwords and firewall protection. And since the advent of networking, computer scientists and engineers have made huge efforts to prevent enormous amounts of information — much of it confidential — from being stolen, deleted or used maliciously.
But computers and the networks connecting them have become more omnipresent and advanced. Now, many systems use open source technology, which allows outsiders to improve the software or change it to fit different needs.
A pattern has emerged: Computer scientists develop a new system. Hackers find ways to compromise it. Computer scientists work to defeat those attacks and develop better security measures. Hackers find ways to defeat them. The cycle continues.
“This is an arms race,” said Dr. Douglas Reeves, professor of computer science.
Cyber attackers can take many forms, but the threats many people in the field are most worried about are called “botnets.” These attackers break into a computer, or a group of thousands of computers, and use the machines to commit a crime, all without the computer’s owner knowing what’s happened. It’s as if someone used a stolen vehicle as a getaway car after robbing a store. A botnet called ZeuS, for example, has been getting plenty of national media attention because it is used to steal bank account usernames and passwords.
But as botnets and other attack programs gain attention, Reeves and others at NC State are working to fight them. Among Reeves’ projects is an effort to help systems recognize when they’re being attacked and build better defenses that don’t inhibit the computer’s performance. Likewise, Dr. Xuxian Jiang, an assistant professor of computer science, is working to better understand how botnets communicate with each other, which could help researchers design systems to stop them.
Much of the security work at NC State is done with the help of the Virtual Computing Laboratory (VCL). When it was introduced at NC State in 2004, the VCL was one of the first large-scale examples of “cloud computing” operating in an educational setting. The technology lets users run software on high-powered servers accessed through their personal computers. This lowers hardware and software costs because it shares resources among its users and readapts itself when new users want to use different sets of applications.
The VCL is an extremely secure system, but NC State computer scientists want to push its boundaries further. Through the new Secure Open Systems Initiative (SOSI), which is supported by the U.S. Army Research Office, researchers are working to develop a hyper-secure version of the VCL that conforms to strict military and governmental regulations.
 The VCL’s security research can also serve the private sector. SOSI develops techniques and tools to secure open systems and helps industry collaborators assess these systems, including trustworthy deployment testbeds. The results, researchers say, will foster economic growth. Partners in the venture include Cisco, IBM, MC Dean, Red Hat and Tekelec.
The VCL’s security research can also serve the private sector. SOSI develops techniques and tools to secure open systems and helps industry collaborators assess these systems, including trustworthy deployment testbeds. The results, researchers say, will foster economic growth. Partners in the venture include Cisco, IBM, MC Dean, Red Hat and Tekelec.
“Given the access to VCL and given our experience in security research, I think we are in the best position to tackle this problem,” said Dr. Peng Ning, associate professor of computer science and technical director of SOSI.
The work is done with the help of students, who get a chance to work in a state-of-the-art computing lab that prepares them for careers in the burgeoning cybersecurity fields. The U.S. government and private companies will need about 60,000 cybersecurity workers over the next three years, according to a Boeing technical director recently quoted in Business Week.
“This provides a perfect environment for us to do our work and observe real-world problems,” said Ahmed Azab, a graduate student who works in Ning’s lab.
The researchers also see great needs for security in health care systems. Health care now accounts for 16 percent of the U.S. gross domestic product, and increasingly complex and interconnected computer systems are needed to manage that hulking pile of information. Dr. Laurie Williams, associate professor of computer science, worries that without proper security measures whole databases could be deleted, or a doctor anywhere in the world could uncover health care information for any patient.
One of Williams’ projects involves studying whether a virtualized, open-source health care computing system could be securely used in rural areas that lack access to centralized servers and maintenance service.
“It’s kind of a dangerous thing because health care is one of the few domains where involuntarily all of our records can be sent all over the place,” said Williams, who leads NC State’s Center for Open Software Engineering. “So it’s very important that the software be very secure.”
Health care is also a field to which students can easily relate, so much of Williams’ coursework involves health-care applications. She has also organized a series of health care information technology forums that have brought together health care researchers, academics and practitioners to foster partnerships and collaboration.
Bringing people together is also a responsibility that Dr. Annie Antón has assumed. Antón, a professor of computer science, works on ways to make the often-convoluted language of privacy policy more understandable for non-computer scientists. She directs the Privacy Place, a privacy research center that aims to disseminate privacy information to the public, software developers and lawmakers.
Antón says that software engineers, for example, aren’t trained to analyze law so they can ensure that the software they write follows the law. She works to bridge those gaps, which includes testifying before Congress on privacy issues.
“Unless we make sure that we are disseminating that knowledge to the lawmakers, we’re never going to improve things for our nation,” Antón said. “Things change, and it’s all about making sure Congress is informed.”
Keeping computer networks secure is the focus of researchers in the Department of Electrical and Computer Engineering. Dr. Wenye Wang, an associate professor, leads a laboratory that is working on a host of network security projects, including assessing the security of power grids and designing self-healing networking architecture that can withstand the havoc caused by a weapons of mass destruction attack.
The lab is also working on the first networking communications backbone of the FREEDM Systems Center, a National Science Foundation Engineering Research Center headquartered at NC State that’s working on ways to bring the “smart grid” into homes, vehicles and businesses nationwide.
The nature of cybersecurity work means researchers are constantly adapting to more complicated systems — and more complicated attacks. The arms race continues.
“To work in this area,” said Dr. Mladen Vouk, head of the Department of Computer Science, “you can’t really relax.”
###
Return To News Homepage